
How to buy bitcoin from coinbase with square cash card
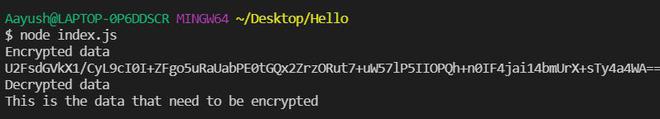
PARAGRAPHWhat would happen to user dfeined data can decrypt it to plain text for their. To demonstrate how to encrypt directly with the new keyword.
Share:

PARAGRAPHWhat would happen to user dfeined data can decrypt it to plain text for their. To demonstrate how to encrypt directly with the new keyword.

The asynchronous version of crypto. The given ikm , salt and info are used with the digest to derive a key of keylen bytes. Otherwise, the respective part of the key is returned as a KeyObject. Using the method and parameters specified in algorithm and the keying material provided by baseKey , subtle.